The Roman legions conquered the known world. We're still using their playbook—and it's killing us.
After three decades building security software, I’ve learned that the most useful insights about our industry often come from unexpected places. For me, one of those places is the Roman Empire — its military doctrine, its organizational genius, and the lessons it still holds for anyone building systems designed to defend against persistent, adaptive adversaries.
The more I’ve studied Roman legions, the more I’ve come to an uncomfortable realization: the modern Security Operations Center is still organized around a warfare model that’s over two thousand years old. And while that model was brilliant for its time, the enemy we face today doesn’t play by the same rules.
Rome’s Tiered Defense
During the Roman Republic, the legion operated under what historians call the manipular system — a tiered battle formation that was arguably the most sophisticated tactical structure in the ancient world. I’ve spent years reading primary sources on this, from Polybius’s firsthand accounts to Livy’s histories, and the elegance of the design still strikes me.
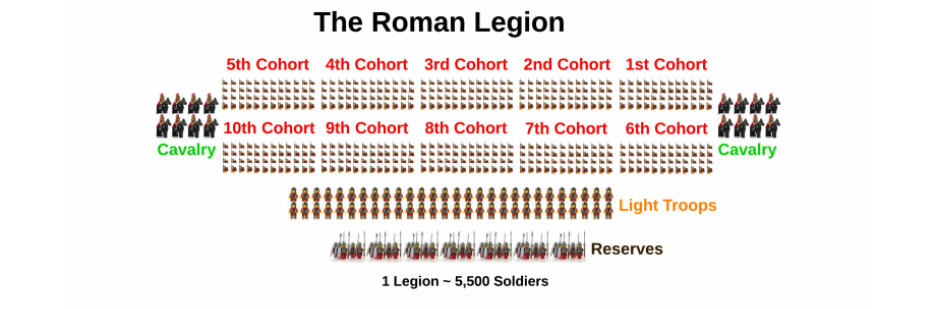
The Romans arranged their infantry in three successive lines.
- The hastati — the youngest soldiers — stood in front, absorbing the initial shock of combat.
- Behind them, the principes — men in their prime with real combat experience — waited to rotate forward and hit an already-fatigued enemy with fresh troops.
- In the rear stood the triarii — the oldest, most seasoned veterans, armed with long spears as the line of last resort.
The Roman expression “res ad triarios venit” (it has come to the triarii) — was an idiom for desperation. In SOC terms, it’s the moment someone says “page the CISO now!”.
The genius of the legion’s formation was rotation. Unlike a Greek phalanx committed all at once, the Romans fed fresh lines into the fight sequentially. An enemy who had just exhausted themselves breaking through the hastati would suddenly face completely fresh principes. It was devastating against all enemy, and it conquered the known world.
The SOC Inherited the Playbook
The structural parallel to the modern SOC is almost uncanny. Tier 1 analysts are your hastati — junior, absorbing the initial flood of alerts, triaging and deciding what gets escalated. Tier 2 analysts are your principes — applying deeper analysis, correlating across data sources for the cases that get escalated from Tier 1. Tier 3 analysts are your triarii — the senior experts called in when things have gotten serious.
This has been the default organizational model for as long as I’ve been in this industry. At a surface level, it makes intuitive sense: efficient use of scarce senior talent, progressive escalation, structured response.
But here’s where the analogy — and the model — breaks down completely:
The Enemy Doesn’t Get Tired Between Tiers
The manipular system worked because the enemy was a physical force subject to exhaustion. By the time the principes stepped in, the opposing army was fatigued, bloodied, and demoralized. The system exploited the physics of human endurance.
Unlike brutal battles of the past, threat actors don’t get tired while your alerts move from Tier 1 to Tier 2.
When a SOC analyst escalates an alert, they apply no friction, no attrition on the attacker. The time spent in escalation queues — the handoffs, the context-gathering, the re-investigation at each tier — works entirely in the adversary’s favor. Every hour an alert spends moving through your tiered process is an hour the adversary spends moving laterally and deepening their foothold. For example, a credential compromise detected at 9 AM might reach Tier 3 at 2 PM the same day. By then, the attacker has accessed 47 additional systems, exfiltrated customer data, and established three persistence mechanisms. So, your SOC process didn't slow attackers down, it gave them a five-hour head start!
The Roman model assumed successive engagement degraded the enemy. In cybersecurity, successive escalation degrades the defender.
By the Time a Case Reaches Tier 3, It’s Already a Mess
When a case finally reaches your most experienced analysts, it doesn’t arrive as a clean, well-scoped problem ready to be dispatched by expert hands. Context has been lost across handoffs. Initial triage decisions were made without visibility into adjacent signals. The adversary has had time to pivot from the initial compromise into identities, systems, and data stores that weren’t part of the original alert. The attack you identified with the initial detection liked morphed into something entirely different.
Your Tier 3 analysts aren’t stepping into a battle where the enemy has been softened up by the lines in front of them. They’re stepping into a situation where the adversary has been inside the walls for hours or days, has established multiple positions, and has had time to cover their tracks. Their job at this point is to document a breach, not stop it.
The Roman triarii were a steadying force at a decisive moment, and that’s what made them effective. Your Tier 3 analysts are playing catch-up against an adversary who has used your own process against you.
The Tiered SOC Structure Itself Is the Bottleneck
Even the Romans eventually abandoned the manipular system as they faced new adversaries that the system wasn't designed for like Germanic tribes that refused static battles and Numidian cavalry that struck and vanished. After the Marian reforms (the fundamental restructuring of the Roman military by consul Gaius Marius) of 107 BCE, the three-line structure was replaced by cohorts — standardized, professional, interchangeable units where every soldier was equipped and trained to the same standard. The Romans recognized that battlefield complexity demanded more flexible, more uniformly capable formations.
The SOC hasn’t had its Marian reform yet.
The tiered model creates three compounding problems:
- It delays expertise — the most capable analysts are engaged last by design.
- It fragments context — every handoff breaks the subtle connections that only become visible when you look across identity providers, cloud platforms, and endpoint systems simultaneously.
- It creates a false sense of thoroughness — an alert that passes through three tiers feels rigorously analyzed, but if each tier is looking at the same narrow slice of data, you’ve just had three people look through the same window.
It’s Time to Evolve the Tiered SOC Structure
The answer isn’t to flatten the SOC into a structureless mass. Experience and specialization matter. The answer is to stop using the tiered structure as the primary mechanism for determining investigation quality.
What if every investigation began with the same comprehensive, cross-platform baseline — regardless of which analyst initiated it? What if the questions a 20-year veteran would think to ask were encoded into the investigative process itself? What if context from across your identity providers, cloud platforms, and endpoint systems was automatically correlated at the moment of initial triage — not hours later after two escalations and a ticket transfer?
This is the fundamental premise behind Command Zero. We encode the investigative methodology of senior analysts into repeatable, automated sequences. When a Tier 1 analyst initiates an investigation on our platform, they’re executing the same comprehensive, cross-platform investigation that your most experienced analyst would conduct. The investigation doesn’t need to cascade through three tiers to reach the right depth. It starts at the right depth.
The Romans didn’t cling to structures that had been outpaced by the battlefield. Their willingness to evolve — from phalanx to maniple to cohort — is what made them dominant for centuries. The goal isn’t to eliminate SOC tiers — it’s to make them irrelevant to investigation quality. When every analyst can battle adversaries at the depth of your best, the tiers become a management structure, not an investigative bottleneck.
The Romans’ greatest strength was never a particular formation. It was their willingness to abandon what had made them great when the battlefield demanded something new. That is the reform the SOC is overdue for.







